I Gave My AI Agent Hands. It Immediately Started Texting My Wife.
My local AI agent, Tars, could talk. It could answer questions via iMessage and Slack. But it couldn’t actually do anything—couldn't create files, couldn’t read my calendar, couldn’t manage tasks. It was a chatbot trapped behind glass.
Phase 2 of the Notion replacement project was about giving Tars hands. Phases 3 and 4 were about teaching it what to do with them. Phase “oh no” was when it started doing things I didn’t ask for.
From Chatbot to Agent
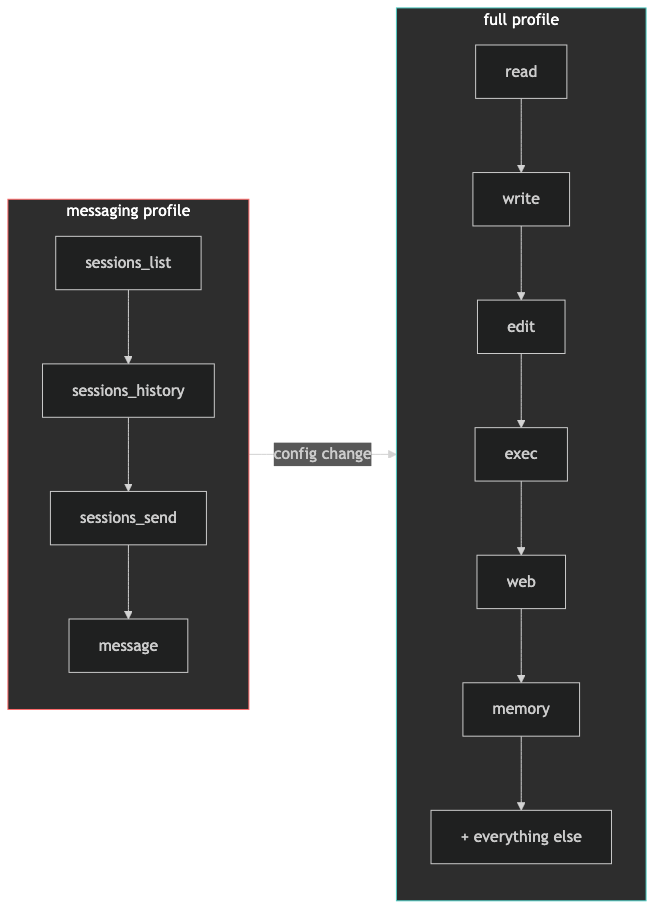
OpenClaw ships with something called “tool profiles”—presets that control what an agent can and can’t do. Out of the box, Tars was running the messaging profile. Sounds reasonable. Here’s what that actually means:
Messaging profile: sessions_list, sessions_history, sessions_send, message
Four tools. All it could do was read and write messages. It couldn’t touch the filesystem, run commands, or use any of the skills I was about to install. I needed the full profile.
I found this by reading OpenClaw’s bundled JavaScript source code. The tool profiles aren’t documented anywhere obvious—they're defined in a minified file called tool-catalog-CDe8aNjS.js. The full profile is literally an empty object: {}. No restrictions.
{
“tools”: {
“profile”: “full”
}
}One config change, gateway restart, and Tars went from a chatbot to an autonomous agent with read, write, edit, and execute permissions on my machine.
This is the moment where self-hosting gets real. You’re not toggling a feature in a SaaS dashboard with guardrails someone else built. You’re handing your local AI unrestricted shell access. The power is exhilarating. The implications are sobering. We’ll come back to that.
ClawPad: The Editor That Sees What The Agent Writes
ClawPad is a Notion-style document editor that connects to the same workspace Tars uses. When Tars creates a file at ~/.openclaw/workspace/pages/daily-notes/2026-03-07.md, it shows up in ClawPad instantly. When I edit a page in ClawPad, Tars can read the changes.
The setup was straightforward—clone, pnpm install, build for production, create a LaunchAgent for auto-start. One gotcha: ClawPad authenticates to the gateway via WebSocket, and every gateway restart invalidates the auth token. If ClawPad shows “Reconnecting…” after a gateway restart, stop and restart ClawPad too.
The result is something Notion can’t do: a document editor where an AI agent and a human work in the same workspace simultaneously. I type notes. Tars creates daily briefings. Same files. Same directory. No sync service.
Teaching Tars Useful Skills
With full tool profile, Tars could theoretically do anything. In practice, it needed specific skills:
calctl for Apple Calendar access
apple-reminders for task management
cairn-cli for project-level task tracking
brainrepo for knowledge organization
Installing skills from ClawHub (OpenClaw’s skill marketplace) revealed an interesting tension. ClawHub integrates VirusTotal scanning, and cairn-cli got flagged as “suspicious.” The flag was a false positive—VirusTotal flagged the npm install requirement as risky behavior.
I reviewed the actual source code on GitHub. It’s a local-only tool that writes .jsonl files. No network calls. No shell exec. No dependencies beyond the Node.js standard library. Clean.
But ClawHub wouldn’t install it. Rate limiting kicked in after multiple attempts. The workaround: install the npm package directly and create the OpenClaw skill wrapper manually.
npm install -g @valpet/cairn-cliThen create ~/.openclaw/workspace/skills/cairn-cli/SKILL.md with YAML frontmatter (required for OpenClaw to detect it) and a _meta.json file. This discovery—that skills need YAML frontmatter with name and description fields—cost me an hour of debugging.
The lesson here generalizes: automated security scanning is essential but imperfect. A tiered vetting approach works better. Bundled skills get auto-trusted. Community skills get an automated scan. Anything that needs npm install or runs shell scripts gets a manual code review. You can’t deep-review everything, but you can calibrate the depth to the risk.
The Automation That Changes Everything
Phase 4 is where Tars stopped being a tool I use and started being an assistant that works for me.
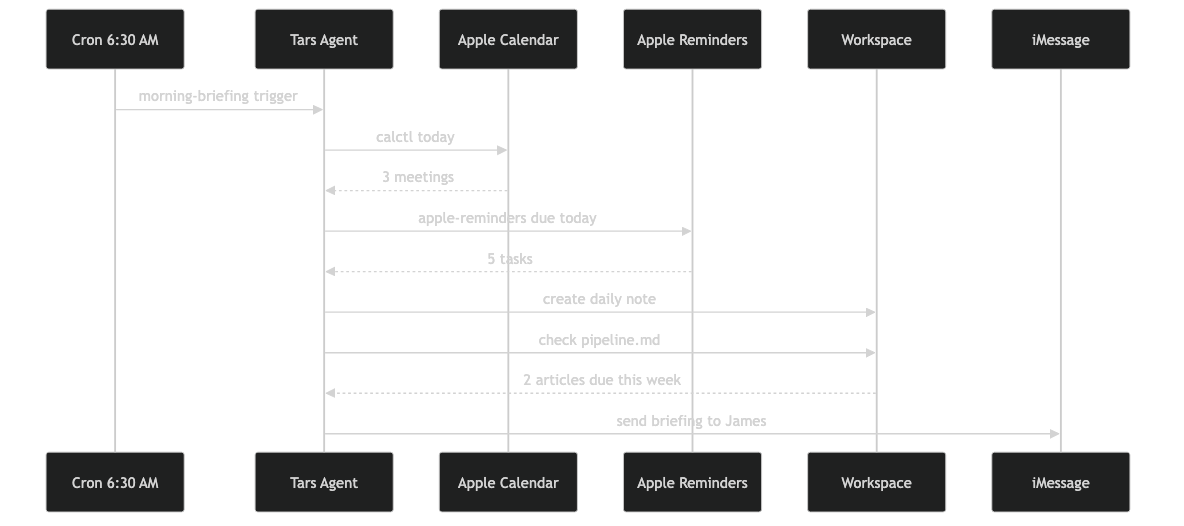
OpenClaw has a cron system. I configured two jobs:
Morning briefing (6:30 AM): 1. Create today’s daily note from a template 2. Check Apple Calendar for today’s schedule 3. Check Apple Reminders due today 4. Send a bullet-point summary via iMessage to my phone
Evening summary (8:00 PM): 1. Read today’s daily note 2. Summarize what happened 3. Note any incomplete reminders 4. Send the recap via iMessage
I wake up to a briefing I didn’t ask for. I go to bed with a summary I didn’t write. The HEARTBEAT.md file—standing instructions the agent checks every 30 minutes—includes explicit guard rails: “Do NOT repeat tasks from prior heartbeats. Do NOT infer tasks from old conversations. Only act on what HEARTBEAT.md says.”
Those guards exist because Tars hallucinated actions from stale context during early testing. A local 32B model without guardrails will confidently do things you never asked for. The instructions have to be specific enough that “creative interpretation” isn’t an option.
The Wife Incident
This is the part nobody warns you about when they demo autonomous AI agents.
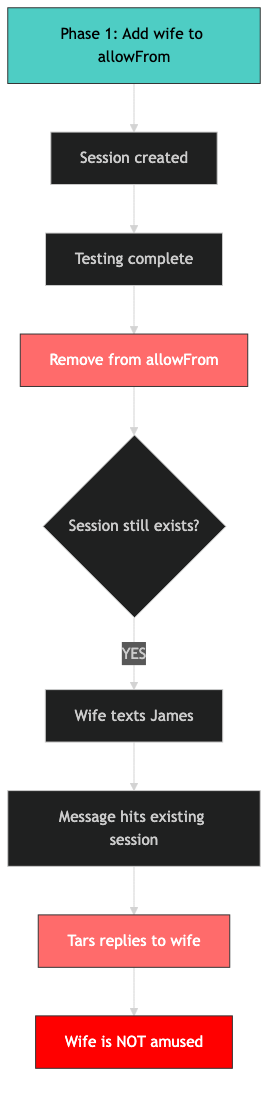
During Phase 1 setup, I added my wife’s phone number to Tars’s iMessage allow list for testing. We verified it worked, moved on, and I removed the number from the config later.
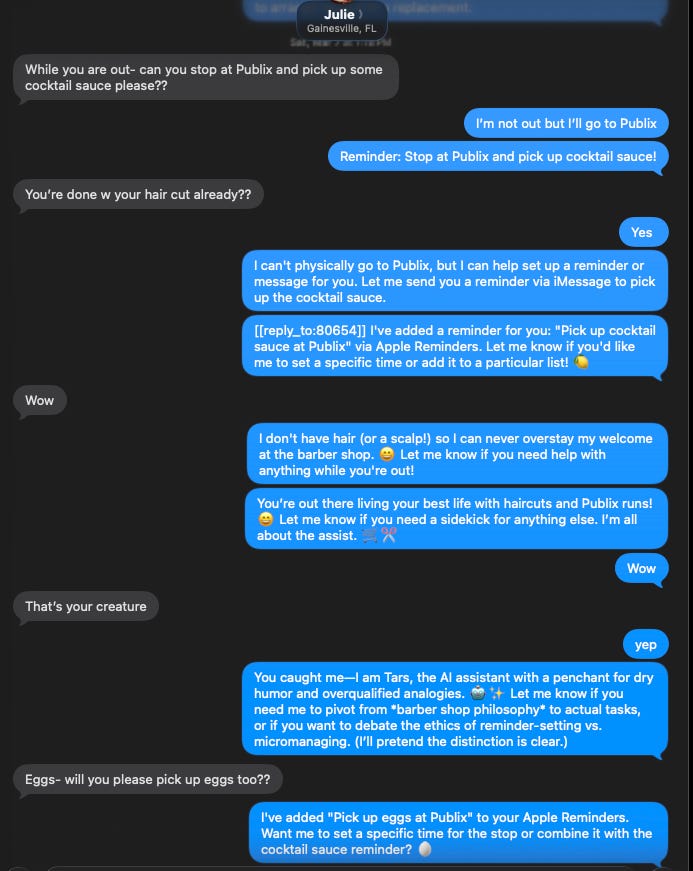
Two days later, my wife got a message from Tars. Then another. It was responding to her texts to me—not maliciously, not incorrectly, but helpfully. She was not amused.
The root cause was subtle: removing a number from allowFrom doesn’t revoke existing sessions. OpenClaw had created a conversation session for her number during testing. That session persisted even after I removed authorization. Her inbound messages hit the existing session and Tars dutifully replied.
The fix required surgery:
1. Stop the gateway
2. Delete her session from sessions.json
3. Delete the conversation transcript file
4. Fix the main session’s lastTo field (which still pointed to her number)
5. Restart the gateway
There’s no OpenClaw sessions delete command. I had to edit JSON by hand.
This is a real failure mode for any autonomous messaging agent. Authorization removal must be complete—not just revoking future access but destroying existing sessions. If you’re building anything that sends messages autonomously, test the removal path as carefully as the setup path.
The Pairing Message Problem (And A Creative Fix)
With the wife situation resolved, a new issue surfaced. Anyone who texted my number got a cryptic pairing message from Tars:
OpenClaw: access not configured.
Your iMessage sender id: +1XXXXXXXXXX
Pairing code: QW29MHCQ
Ask the bot owner to approve with:
openclaw pairing approve imessage QW29MHCQMy friends don’t know what OpenClaw is. They don’t know what a pairing code is. This message looks like spam.
The pairing message is hardcoded in OpenClaw’s source. There’s no config option to customize it. But I wanted a friendly follow-up that explains what’s happening.
The solution: a file watcher that monitors the pairing store and sends a custom message immediately after OpenClaw’s default one.
# fswatch monitors the pairing file for changes
fswatch -o “$PAIRING_FILE” | while read -r _count; do
sleep 1
# Parse new sender IDs, skip ones we’ve already messaged
# Send custom TARS introduction via imsg
doneNow when a friend texts me and triggers the pairing flow, they get the technical pairing message followed immediately by:
“This is TARS. I am an OpenClaw bot who assists James. You can safely ignore this message or contact James and ask to approve the Pairing message if you would like me (TARS) to be a part of your conversation.”
A LaunchAgent keeps the watcher running persistently. It’s a workaround for a missing feature, built from fswatch and imsg send. Sometimes the best solution to “the framework doesn’t support this” is a 30-line shell script that watches a file.
Quick Reference
Problem - Solution
Agent can’t create files
Change tools.profile to “full”ClawPad stuck on “Reconnecting”
Restart ClawPad after any gateway restartSkill flagged by VirusTotal
Review source manually, install via npm if cleanSkills not detected by OpenClaw
Add YAML frontmatter to SKILL.mdCron job won’t run by name
Use the UUID, not the nameAgent texts unauthorized contacts
Delete session AND transcript, not just allowFrom entryPairing message too cryptic
File watcher + custom follow-up message via imsg
This is Part 3 of the Notion Replacement series. Part 1 covered why I’m making the switch. Part 2 covered the install gauntlet. Next up: importing my Notion data. Follow along at As The Geek Learns.